Read This Like an Intelligence Brief
As I outlined in the first article in this series, the CESER FY2026-2030 Strategic Plan is a document with implications for the entire federal cybersecurity community. But one section in particular deserves focused attention: the threat landscape analysis.
CESER defines four distinct categories of threat to U.S. energy infrastructure. I want to walk through each one the way I would with an agency team preparing a briefing, not the way a press release would present them.
Cyber Threats: The One Everyone Knows, but Underestimates
The plan identifies digital control system and network breaches, operational disruptions, data exfiltration, malware, ransomware, and denial-of-service attacks as core cyber threats to the energy sector. None of this is new. What is new is the operating environment.
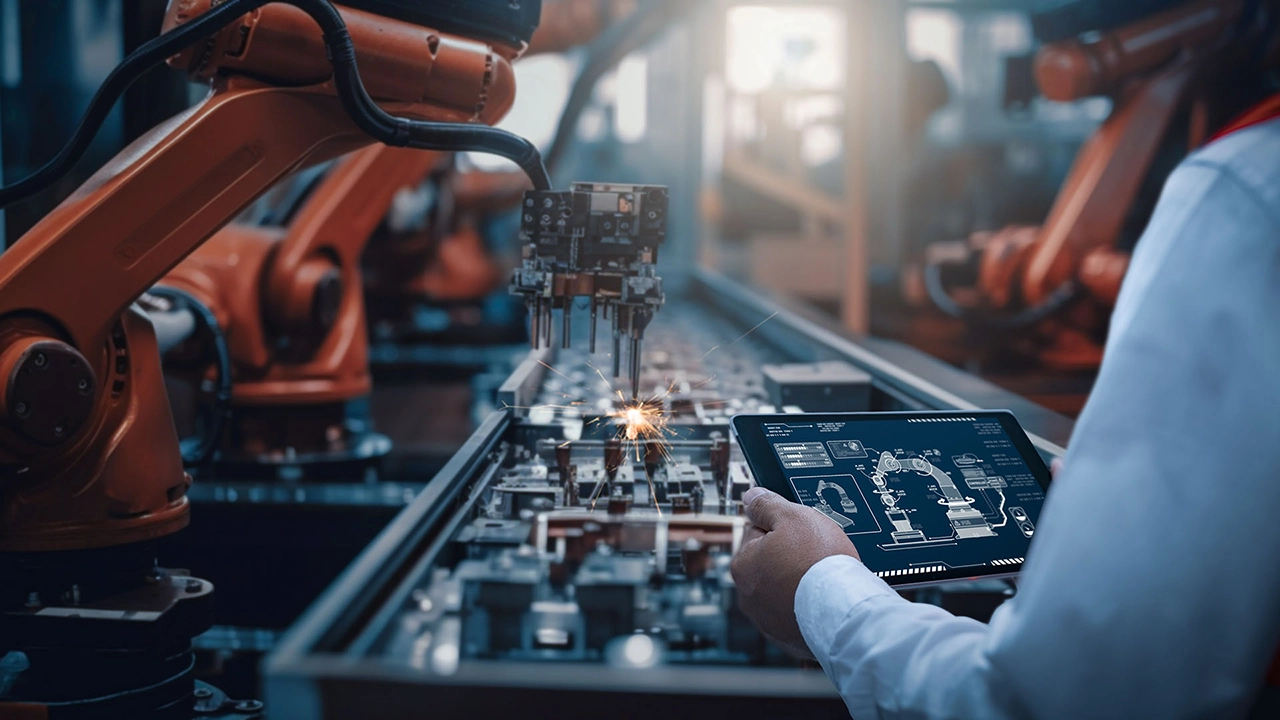
Energy systems are more digitally connected than at any prior point in their history. Industrial control systems that were once air-gapped are now networked. That convergence of OT and IT creates an expanded attack surface that most federal agency cyber programs are not fully equipped to monitor. The threat is not theoretical. It is active.
Physical Threats: Kinetic Risk Is Back on the Table
The plan explicitly names vandalism, sabotage, terrorist attacks, natural hazards, and accidents as physical threat vectors. The inclusion of counter-UAS capabilities in CESER’s hardening programs is not accidental. It reflects a threat environment where physical attacks on grid infrastructure have become a documented and recurring concern.
For federal cybersecurity leaders, physical security and cyber security are no longer separable disciplines.
Economic Threats: The Slow Burn
Market volatility, aging infrastructure, regulatory uncertainty, workforce skill shortages, and supply chain interference are listed as economic threats. These tend to get less attention in cybersecurity conversations because they don’t produce incident reports.
But aging infrastructure creates exploitable vulnerabilities. Workforce shortages leave monitoring gaps. Supply chain interference is how sophisticated adversaries plant long-term access inside critical systems. Economic threat vectors are entry points.
Geopolitical Threats: The Strategic Context Everyone Needs
The plan draws a direct line from international conflicts, civil unrest, political instability, and trade disputes to direct risks to U.S. energy systems and supplies. The Annual Threat Assessment of the U.S. Intelligence Community, cited in the CESER plan, puts it plainly: the severe effects of these threats on U.S. energy systems are expected to escalate as adversaries attempt to shape world events.
Federal cybersecurity leaders who do not account for geopolitical context in their threat modeling are working with an incomplete picture.
How CESER Is Responding
CESER’s Energy Threat Analysis Center functions as a threat intelligence hub where government, industry, and stakeholder partners analyze sensitive information together. The Cybersecurity Risk Information Sharing Program deploys sensors and monitoring solutions to identify threats within energy sector networks in near real time.
The intelligence architecture exists. The question is whether your agency is connected to it.
The next article in this series goes deeper into one of the most consequential gaps in federal energy sector cybersecurity: the OT and ICS security problem.