From Strategy to Action
Over the course of this series, I have walked through what the CESER FY2026-2030 Strategic Plan signals at the big picture level, what the four threat categories mean operationally, where the OT and ICS security gap continues to widen, and how AI is reshaping both the threat and the defense landscape. This final article is about what to actually do with that information.
Federal IT and cybersecurity leaders do not lack awareness of these challenges. What they often lack is a structured way to prioritize action given competing demands, limited resources, and a policy environment that keeps changing. Here are five steps grounded directly in the CESER plan’s priorities.
1. Conduct a Risk-Informed Assessment of Your Energy Dependencies
CESER’s plan reflects a deliberate shift from an “all hazards” posture to a risk-informed one. Start by mapping how your agency depends on energy continuity for mission delivery. Which operations fail if grid power is disrupted? Which systems rely on energy-dependent infrastructure? That dependency map is the foundation for everything else.
2. Close the OT Visibility Gap Before You Address Anything Else
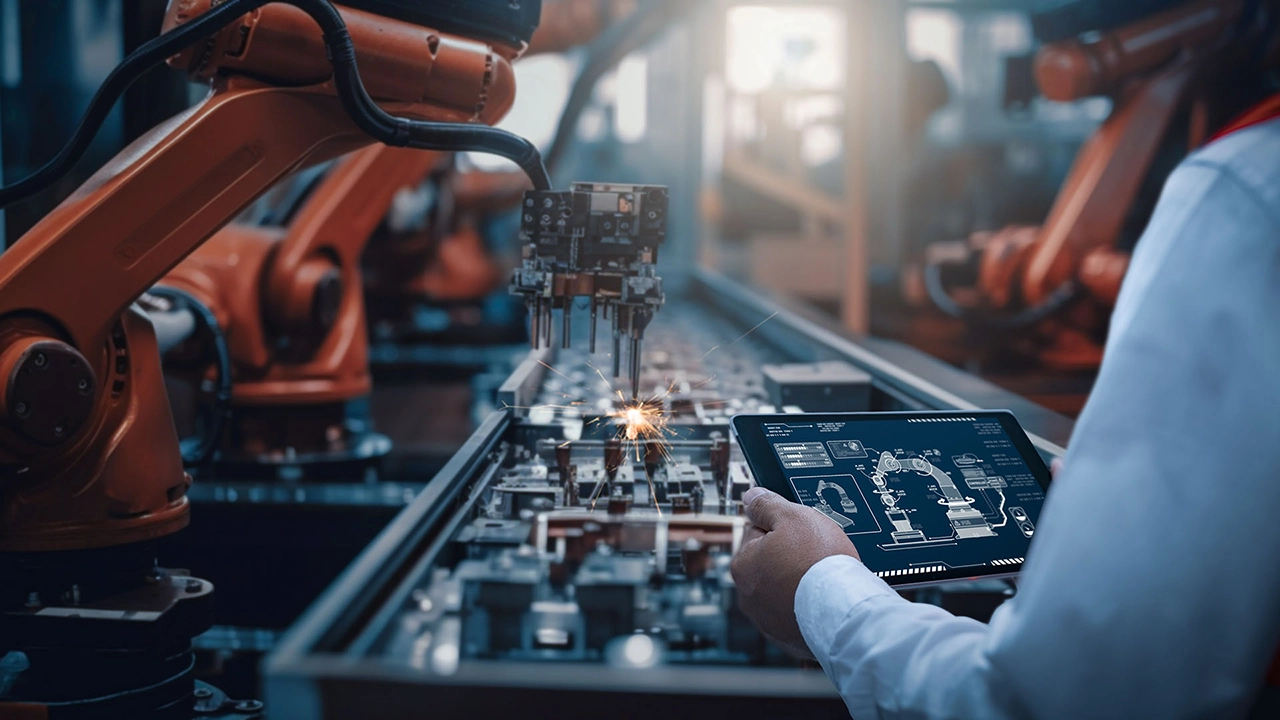
You cannot secure what you cannot see. The CRISP program exists because visibility into OT environments across the energy sector is still insufficient. If your agency operates or connects to systems with industrial control components, begin with a current-state inventory. Know what is in your OT environment, what it talks to, and what monitoring is actually in place.
3. Apply Cyber-Informed Engineering Principles to New Acquisitions
CESER’s Cyber-Informed Engineering program makes a straightforward argument: security should be designed in, not bolted on. When your agency procures new systems with digital connectivity, sensors, or control functions, build cybersecurity requirements into the acquisition process from the start. Review your supply chain for the same issues CyTRICS is surfacing at the sector level.
4. Connect to Threat Intelligence That Is Sector-Specific and Actionable
The Energy Threat Analysis Center and related CESER programs produce threat intelligence designed specifically for energy sector operators and their federal partners. General threat feeds are useful. Sector-specific intelligence tied to the actual systems and supply chains your agency depends on is more useful. If your agency does not have a direct channel to that intelligence, establish one.
5. Build and Test Your Incident Response Posture Before You Need It
CESER’s third strategic goal focuses explicitly on responding to and recovering from incidents. The plan cites exercises like Liberty Eclipse and Clear Path as hands-on mechanisms for testing response readiness. If your agency does not have a current, tested incident response plan that accounts for energy sector disruptions and OT-specific scenarios, that is the most immediate gap to close.
The Through-Line of This Series
The CESER FY2026-2030 Strategic Plan is clear about one thing above all else: the threats to U.S. energy infrastructure are persistent, converging, and escalating. The plan’s guiding principle, to provide timely and actionable information to the energy sector, only works if federal agencies are positioned to receive and act on that information.
Energy sector cyber resilience is not a DOE problem. It is a federal government problem. The agencies best positioned for the next five years will be the ones that treat it that way now.