Understanding the API security challenge is only the first step. The real question is: how do you secure them?
As federal agencies continue to modernize, APIs are multiplying across environments, connecting applications, enabling data sharing, and driving mission outcomes. To secure them effectively, organizations must move beyond traditional security models and adopt a Zero Trust approach designed for today’s architectures.
Step 1: Start with Visibility
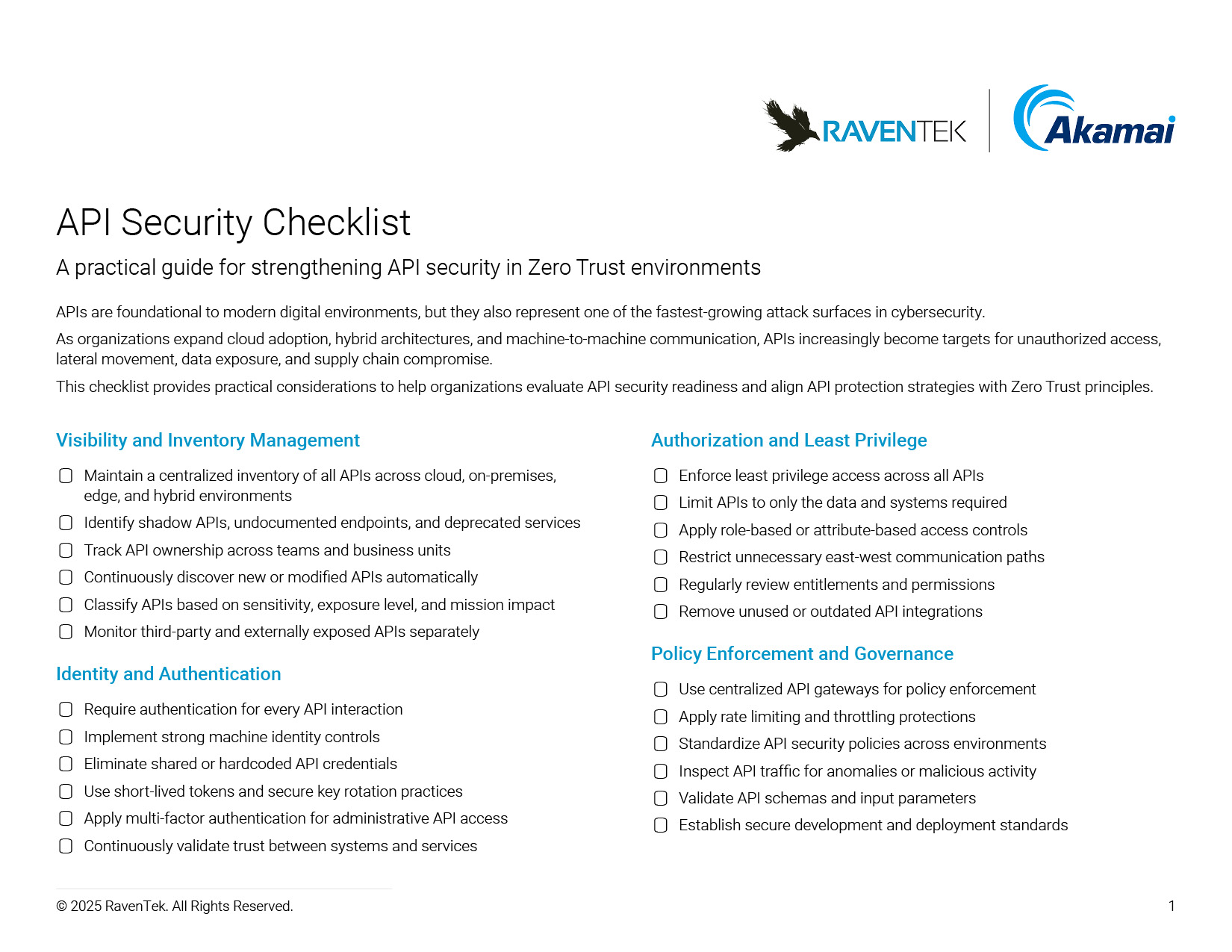
Before implementing controls, agencies need a clear understanding of their API landscape. That means:
- Discovering all APIs across environments
- Identifying shadow or unmanaged APIs
- Building a comprehensive inventory
As Akamai’s Brian Dennis emphasized, “you can’t secure what you don’t know exists.”
Without visibility, every other security measure falls short.
Step 2: Establish Strong Identity and Authentication
APIs require a shift from user identity to machine identity. Organizations must:
- Continuously verify API endpoints
- Authenticate every interaction
- Ensure secure key management
This is especially critical as communication shifts from north-south to east-west traffic.
Step 3: Enforce Policy at Scale
Consistency is key. Agencies should implement:
- Centralized authentication mechanisms
- API gateways for enforcement
- Rate limiting and access controls
This creates a unified control layer across distributed systems, ensuring policies are applied consistently, regardless of environment.
Step 4: Protect Legacy and Hybrid Environments
Legacy systems remain a reality in federal IT. To secure them:
- Use microsegmentation to isolate risk
- “Ring fence” unsupported systems
- Control how APIs interact with legacy infrastructure
These strategies help reduce exposure while enabling continued operation of critical systems.
Step 5: Continuously Monitor and Adapt
Zero Trust is not static. It requires:
- Ongoing monitoring and auditing
- Continuous authorization
- Adaptation to evolving threats
As attacks grow in speed and sophistication, security must evolve just as quickly.
Common Mistakes to Avoid
Many organizations struggle with API security because they:
- Treat APIs like traditional users
- Lack visibility into their environment
- Overexpose API keys or endpoints
- Ignore east-west traffic risks
Avoiding these pitfalls is critical to building an effective Zero Trust strategy.
What Good Looks Like
A mature approach to API security includes:
- Full visibility across all APIs
- Centralized policy enforcement
- Continuous identity verification
- Segmented, controlled environments
- Alignment between security and mission needs
As Keith Busby put it, “security’s an enabler not a barrier.”
The goal isn’t to slow innovation. It’s to enable it securely.
The Path Forward
APIs are essential to the future of federal IT. But without the right strategy, they introduce unacceptable risk. By combining visibility, identity, policy enforcement, and continuous monitoring, agencies can bring APIs into a Zero Trust framework and secure the systems that depend on them.
Put Zero Trust API Security into Action
Take the Next Step Toward Zero Trust API Security
Need help identifying unmanaged APIs, reducing east-west exposure, or strengthening policy enforcement? Schedule a tailored API security assessment with RavenTek and Akamai.




