APIs were built to accelerate innovation. Today, they’re accelerating risk.
Across federal agencies, APIs power everything from data sharing to mission-critical applications. They enable interoperability, support modernization initiatives, and connect systems across cloud, edge, and hybrid environments. But as their use expands, so does their exposure.
In a recent GovCIO panel sponsored by RavenTek and Akamai, federal and industry leaders made one thing clear: APIs are no longer just part of the architecture, they are the attack surface.
APIs Have Changed the Security Equation
Traditional cybersecurity models were built around users and endpoints. Access was largely north-south users connecting into systems. APIs change that.
They introduce:
- Machine-to-machine communication
- East-west traffic across environments
- Dynamic, rapidly evolving connections
As CMS Acting CISO Keith Busby explained, APIs represent “a never expanding, never ending, expanding attack surface.”
That shift has major implications. Security is no longer just about who is accessing systems—it’s about how systems are interacting with each other.
The Visibility Problem: You Can’t Secure What You Can’t See
One of the biggest challenges agencies face is simply understanding their API footprint. Over time, APIs are:
- Built by different teams
- Deployed across multiple environments
- Left undocumented or unmanaged
These “shadow APIs” create blind spots. Organizations may believe they have a few hundred APIs but in reality, that number is often double. Without visibility, securing them becomes nearly impossible.
This is where many Zero Trust strategies break down before they even begin.
Speed vs. Security
APIs are typically developed in fast-moving environments where speed is critical. Developers are focused on delivering functionality, enabling data access, and supporting mission outcomes. Security, while important, is often secondary in the development cycle, and as a result, API keys may be exposed or improperly shared, authentication may be inconsistent, and access controls may be overly permissive.
This creates opportunities for attackers to exploit APIs quickly, often without detection.
Legacy Systems Make It Worse
Federal environments are rarely greenfield. Modern APIs frequently connect to:
- Legacy systems
- Unsupported technologies
- Systems not designed for Zero Trust
This introduces additional complexity and risk. Organizations must secure not only modern architectures, but also the connections between old and new systems, often with limited visibility into how those interactions occur.
What’s at Risk
The consequences of unsecured APIs are significant:
- Unauthorized data access
- Exposure of sensitive information
- Increased lateral movement within networks
- Expanded attack surface for adversaries
And the threat is growing. API attacks are increasing at an unprecedented rate driven by automation, AI, and the expanding digital footprint of government systems.
Why Zero Trust is Essential
Zero Trust fundamentally changes how agencies approach security. Instead of trusting anything inside the network, it assumes:
- Breach is inevitable
- Every interaction must be verified
- Access should be continuously evaluated
As CISA CIO Bob Costello described, Zero Trust means authenticating “every user, every action, every device, everything that occurs, across your network constantly.”
For APIs, this means:
- Treating every API call as untrusted
- Continuously verifying machine identities
- Limiting access to only what is necessary
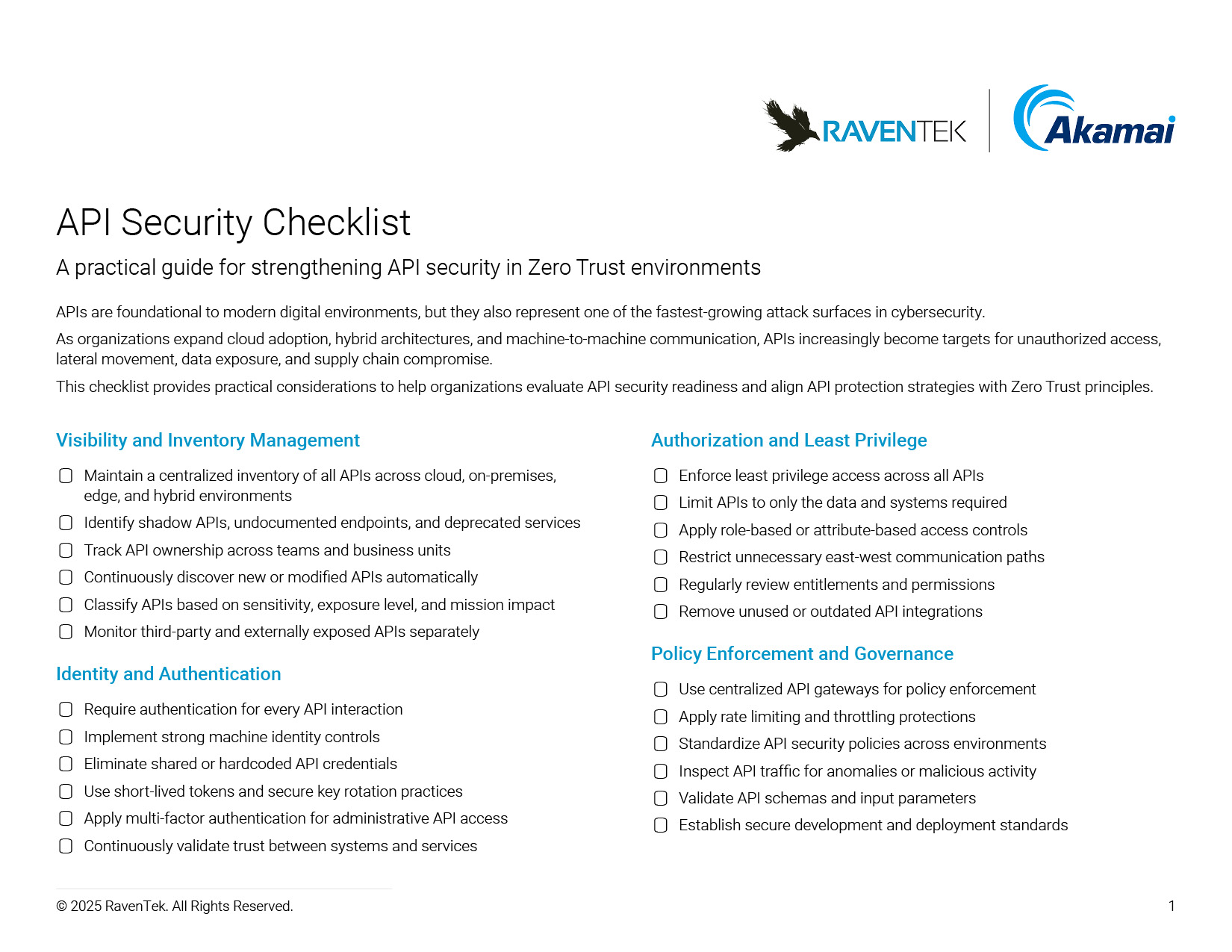
APIs are foundational to modernization, but they also represent one of the greatest security challenges agencies face today. Without visibility, governance, and continuous verification, they become an open door for attackers.
The good news: Zero Trust provides a path forward. But it starts with recognizing that APIs are not just infrastructure. They are critical security assets.
Evaluate Your API Security Posture
See Where Your API Security Gaps Exist
RavenTek and Akamai help organizations uncover shadow APIs, evaluate Zero Trust maturity, and identify practical ways to reduce API-related risk across hybrid environments.




